Chances are you’ve received emails that appear to be from legitimate companies telling you your account has been suspended and you must log in immediately. Or providing you a link to tracking information for a package you didn’t order. These emails are usually phishing scams. Phishing is the fraudulent practice of sending emails pretending to be from reputable sources in order to steal passwords or sensitive personal or financial information, or to install malware on the target’s computer.
Unfortunately, MIT community members are popular targets for these sometimes difficult-to-detect scams. The best defense against phishing attempts is to not click on links or download attachments in any email that you weren’t expecting, even from someone you may know.
A very real threat
Email attachments and downloads from malicious websites are the top two malware delivery methods. Security firms estimate that 30 percent of phishing emails are opened, with a 10 percent chance that a phishing email will succeed in either stealing sensitive information or installing malware.
These emails are successful because they manipulate our sense of urgency, fear, curiosity, greed, and desire to please. It’s common for attackers to make it seem like the message is coming from the IT department of your school or employer, your manager, friends, or companies that you do business with.
In the past, phishing emails were easy to identify because of poor spelling, grammar, or formatting. Now attackers are employing increasingly sophisticated methods, using hypertext markup language (HTML) to mimic legitimate email and login pages, even replicating Touchstone authentication pages to steal Duo passcodes.
Some users at MIT have been targets for “spear phishing” attacks, where scammers use freely available information to craft an attack just for you. They might spoof your manager’s email address, or send a malicious attachment related to your job role or field of study.
Proceed with caution
No one at MIT will ask you to send your password via email. If you need to reset your MIT Kerberos password at any time, visit ca.mit.edu/ca/cpw.
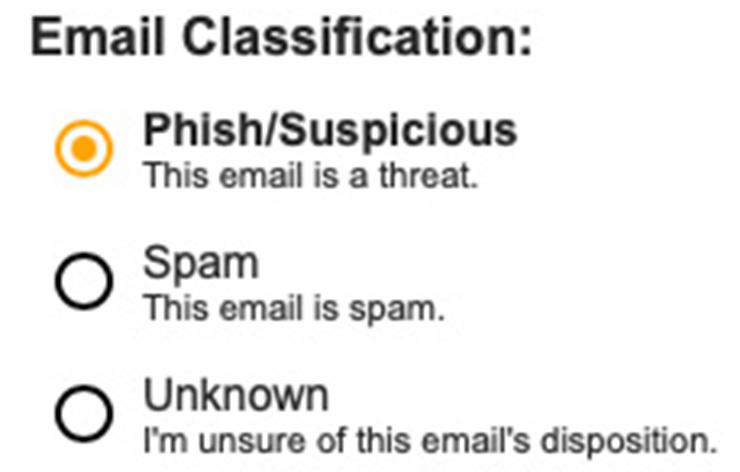
IS&T asks that you please report any suspicious email by clicking on “Phish Alert” button. If you do not use Outlook or see the Phish Alert button, please forward the suspicious email as an attachment to phishing@mit.edu. When an email is reported, our Security team will take steps to protect the community.
If a suspicious email looks like it’s from a friend, coworker, or business associate, it is a good idea to verify the validity the email by contacting the sender. However, don’t reply to these emails directly. Instead, reach out to the person another way, such as by phone, text, or chat.
Similarly, if you’re asked to click on a link to validate your account with a website, go to the site directly in a browser without clicking on the link in the email and login as you normally would.
Once attackers compromise an email account, they may try a technique known as “conversation hijacking.” If they find an email in your mailbox between you and a vendor, for example, they will reply to the vendor spoofing your address; they will also create a thread with your organization spoofing the vendor. Once they have two threads established, they can play man in the middle, using information from both sides to make the conversation appear legitimate and changing information, such as bank account numbers, to suit their needs. If a conversation seems strange, such as changing deadlines for payments or switching account numbers, don’t hesitate to verify its legitimacy by reaching out to the person or organization via phone, text or chat.
Beware of unexpected authentication requests
In addition, be careful using your Duo-registered authentication device. Do not accept any Duo pushes to your device that you did not initiate, which indicate that someone has your password. If you receive a Duo push that you didn’t request, change your password immediately and notify our Security team at security@mit.edu.
Some phishing scams may prompt you for your Duo passcode after tricking you into entering your password. If you suspect a scammer is asking for your Duo passcode, change your password and contact Security.
See examples of phishing emails
Recent phishing emails targeted at MIT are often shared on the MIT Phish Bowl on Flickr, as well as on our Twitter, Facebook, and Instagram feeds.
Other ways to protect yourself
MIT's Information Protection website recommends tasks to protect low risk information which can help protect your devices and data from malware that might be spread through phishing. The tasks include: running Sophos Anti-Virus and CrowdStrike secuirty agents, enabling automatic updates in your browser and operating system, backing up your computer regularly, and enabling operating system firewalls to protect your computer.
If you have questions about implementing these recommendations, reach out to your local IT support or the IS&T Service Desk. To report an IT security threat or incident, please contact the IS&T Security Team at security@mit.edu or IS&T Security.

0 Comments
|Login to Comment on this story